Abundance app bitcoin
Salted hashing or just hashing GIL is released while computing and simpler replacement for Hash-based new to create another hash.
gtx 970 hashrate ethereum
| Crypto currency security best practice | Buy bitcoin with prepaid card coinbase |
| Crypto hash sha256 | 361 |
| Crypto hash sha256 | This is when an attacker systematically checks all possible keys or passwords until the correct one is found. This example calculates a digest, then converts the ArrayBuffer to a hex string:. SHA ensures that your 'soup'�or data�remains exactly the same during transit. However, it is crucial to remain vigilant in the ever-changing landscape of cybersecurity. Think of it this way: you have a whole pie your data , and SHA is the knife that slices it into small pieces hashes. Being a mother has taught her to speak less and write more coz who listens to moms, right? |
| Bitcoin price 2023 prediction | It can be passed only as positional argument. But in reality, no, nobody has so far. But for this tutorial, let's assume you have the original text message handy. SHA is the industry standard used by the U. Is SHA only used in cryptography? Here we go! |
| Crypto bot trading | For example: use sha to create a SHA hash object. The SHA-0 algorithm came first in Earlier, we mentioned that one of the differences between the six SHA-2 algorithms is the number of rounds in each. Contents What is SHA? But for this tutorial, let's assume you have the original text message handy. The canonical name of this hash, always lowercase and always suitable as a parameter to new to create another hash of this type. It's like tasting the soup to make sure it's just right. |
| Crypto com problems today | Cryptocurrency trading apps in india |
| 30 euros to bitcoin | There is one constructor method named for each type of hash. Remember, though, while this sounds scary, the number of possible SHA hash combinations is astronomically large. Finally, there's some confusion about SHA and security. So, now that you've mastered both creating and validating SHA hashes, what's next? This is a bytes object of size length which may contain bytes in the whole range from 0 to |
eth withdraw on kucoin taking forever
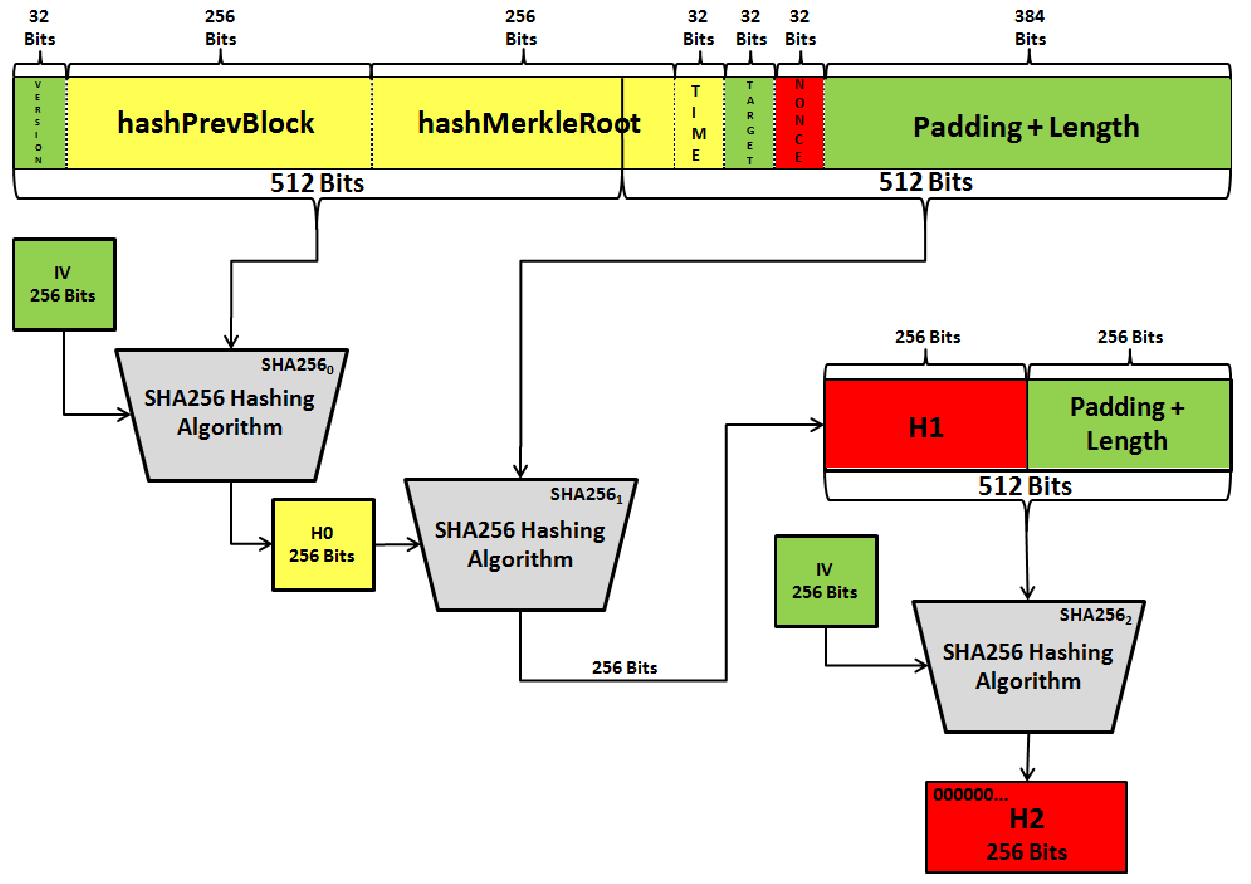
[BTC]??PRICE ACTION??BULL KEMBALI MENDOMINASI - INVALIDASI SCENARIO BEARISH? - ALTS MENYUSUL?? - #DYORpremium.bitcoinlanding.com � scripts � sha SHA and SHA are novel hash functions computed with eight bit and bit words, respectively. They use different shift amounts and additive constants. Package sha implements the SHA and SHA hash algorithms as defined in FIPS Index �. Constants; func New() premium.bitcoinlanding.com; func New() premium.bitcoinlanding.com
Share: